Endpoint Threat Protection
AVAILBLE ON THE SPYCLOUD CONSOLE
Endpoint Threat Protection Overview
Endpoint Threat Protection provides visibility into devices infected with infostealer malware and the credentials harvested from those infections.
When malware runs on a device — whether corporate-managed, unmanaged, contractor-owned, or remote — it can extract saved passwords, session cookies, browser data, and application credentials. SpyCloud recaptures this malware data from the criminal underground and surfaces infection evidence tied to your organization.
The result: extended visibility into workforce identity exposure beyond traditional endpoint tools.
👀 What You Can See
Endpoint Threat Protection identifies:
- Infected devices associated with your workforce
- Malware families responsible for credential theft
- Applications where credentials were captured
- Per-device credential exposure, including usernames, emails, and passwords
- Session cookies that may enable authenticated access reuse
This provides a device-centric view of identity threats — showing exactly which machines exposed credentials and where those credentials may be used.
🧠 Why Visibility into Malware Data Matters
Infostealer malware does more than infect a machine. It extracts identity data that can be:
- Reused across corporate and third-party services
- Sold or traded in underground markets
- Leveraged for account takeover or session hijacking
Many infections occur outside traditional visibility boundaries — on unmanaged devices, contractor machines, or personal systems used for work access.
Endpoint Threat Protection extends visibility into these identity exposures by recapturing and structuring malware-derived credential data tied to your watchlist identifiers.
🧭 Core Views
The module is organized into two primary views:
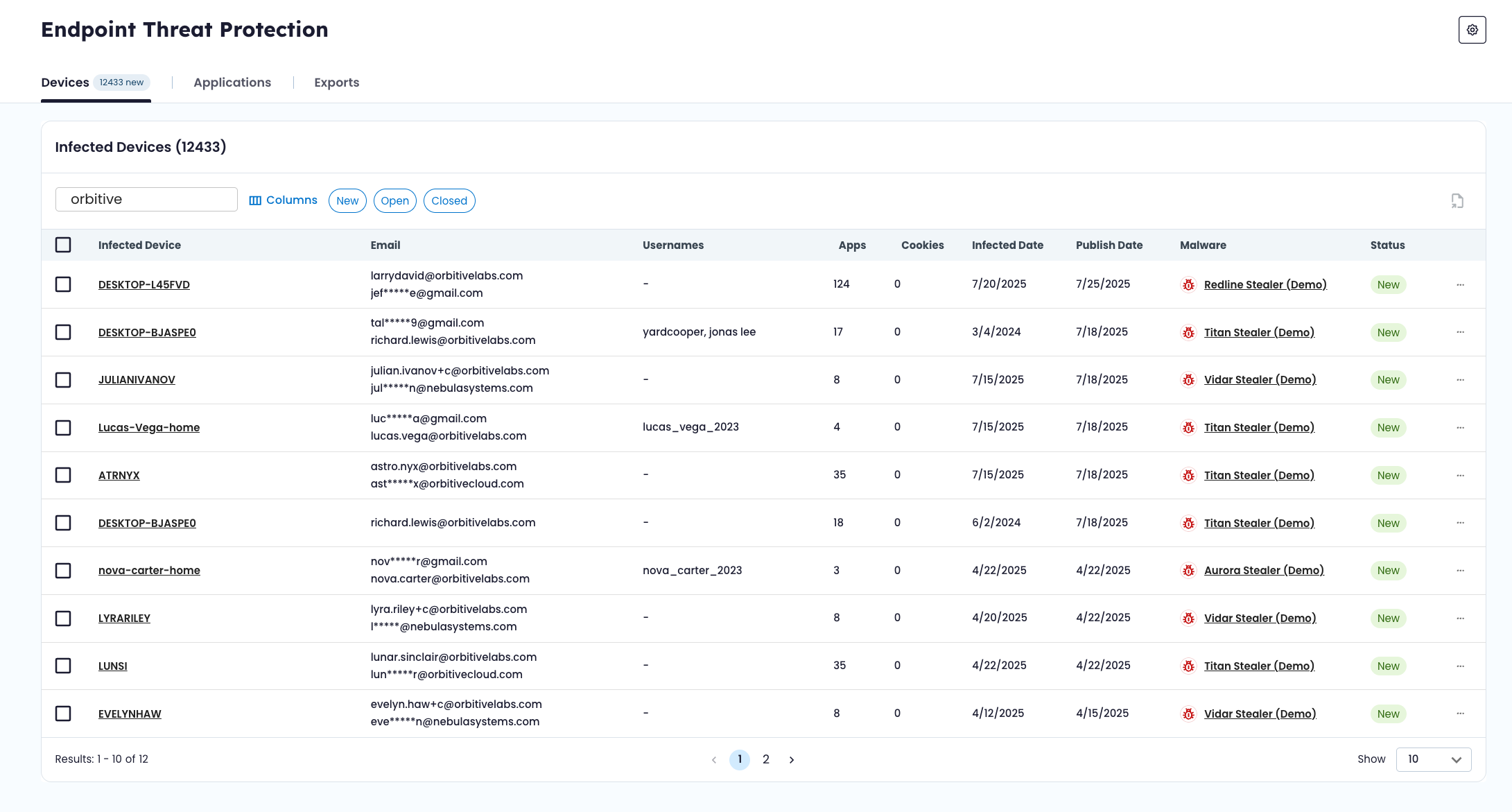
💻 Devices
A device-centric view of infection events, including:
- Hostname and system owner
- Malware family
- Infection and publish dates
- IP and geolocation data
- Exposed applications and credentials
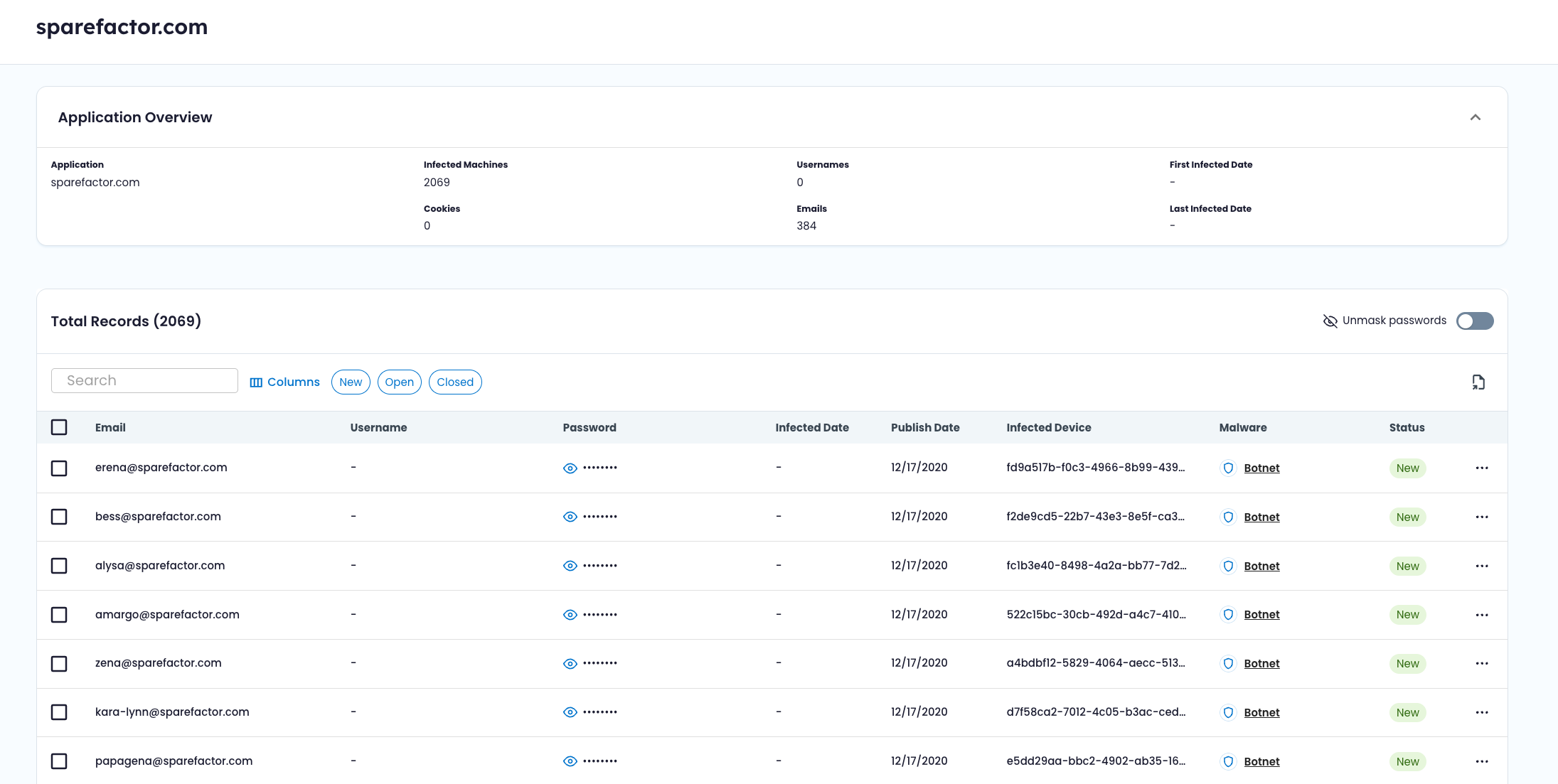
🧩 Applications
An application-centric view showing:
- Domains or services where credentials were harvested
- Number of affected devices
- Counts of usernames, emails, and cookies
- Watchlist status (Verified, Unverified, or No)
Together, these views help you understand both the source of exposure (device) and the potential impact surface (application).
🔗 How Data Is Scoped
Endpoint Threat Protection uses the same shared watchlist as Workforce Threat Protection.
When recaptured malware logs contain credentials or application domains that match your verified watchlist identifiers, associated devices and applications become visible in the module.
For detailed matching behavior and backfill logic, see Watchlist & Data Association.
Updated about 2 months ago