Acting on Supply Chain Exposures
SpyCloud offers workflows to take action on exposed identity data within your third-party ecosystem
👇INVESTIGATE EXPOSURES DIRECTLY FROM SUPPLY CHAIN THREAT PROTECTION

When Supply Chain Threat Protection identities an organization with known exposures, use Investigations to dig deeper into that company's domain and understand what identity exposures could mean for your organization.
Supply Chain Threat Protection ➜ Cybercrime Investigations
From a partner’s Company Detail page in Supply Chain, select Investigate to jump into Investigations with key fields already filled out.
What you’ll get
- Direct handoff from Company Detail to Investigations
- Pre-populated* asset type + asset field (the selected company's domain)
✅ Required Licenses
Access depends on your SpyCloud Investigations license:
- If entitled: you’ll be routed into SpyCloud Investigations
- If not entitled: you’ll see an in-console error message
**👇INVESTIGATE AT THE COMPANY DOMAIN LEVEL **
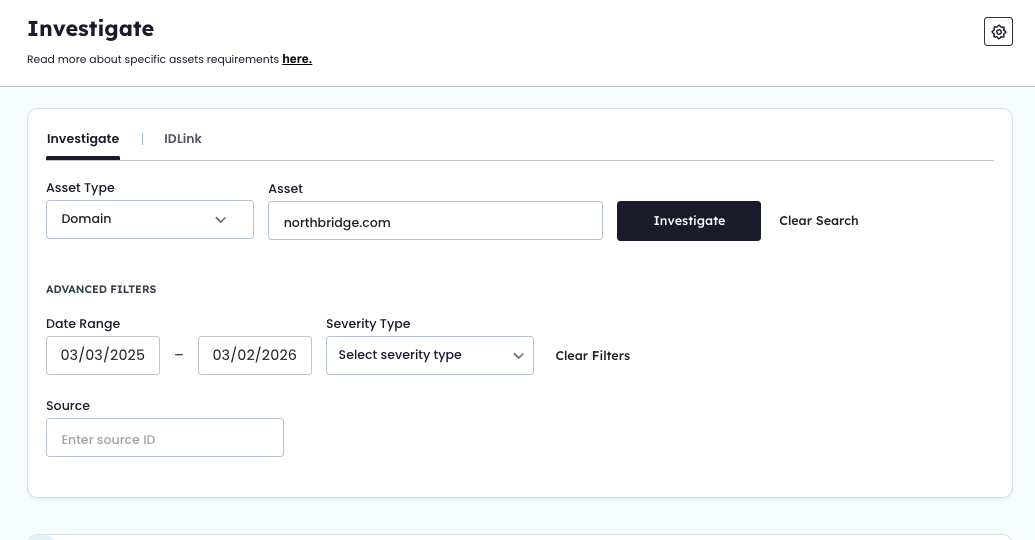
🧭 How to Investigate a Company's Domain
- Go to Supply Chain Threat Protection
2. Open the partner’s Company Detail page
3. Click Investigate in the page header
🔍 What to Do in SpyCloud Investigations
Once you’re in SpyCloud Investigations, you can:
- Review identity exposures tied to the partner’s domain
- Assess potential downstream risk to your organization
- Decide whether additional monitoring or remediation is needed
Updated 3 months ago